Interconnected systems, digitalization, and IoT are key drivers of success for millions of manufacturing companies worldwide. However, this also leaves the door open to cyberattacks that, in addition to financial losses, put people’s lives and environmental health at risk. We analyze this trend and offer some recommendations to protect people, equipment, and the environment.
By Alimey Díaz, Journalist / Technical Writer
Data protection remains a key issue in 2026. As a result of interconnectivity, wireless devices, and IoT, organizations have vast amounts of data available for use in implementing and monitoring asset management strategies and maintenance processes. Protecting this information is crucial to the success of any company.
Within an interconnected factory, cybersecurity is just as important as physical and tangible security, especially as the threat of cyberattacks continues to rise. In this article, we address this approach to cybersecurity behind closed doors, particularly in the manufacturing industry, and outline the key considerations.
“The Manufacturing Security Report,” presented by checkpoint.com https://engage.checkpoint.com/2025-cpr-manufacturing-report/ explains that in 2025, the figures for cyberattacks in the manufacturing industry showed significant numbers:
- 1,585 weekly attacks
- 30% increase in attacks compared to 2024
- 22% of last year’s ransomware victims were from the manufacturing sector.
Ransomware is malicious software that blocks access to files, devices, or networks, and demands payment in cryptocurrency from the organization or individual affected by the lockdown to unlock them. This malware renders the information unusable, under the threat of deletion or disclosure by the hackers if the payment is not made.
According to this FBI report “ransomware attacks can cause costly disruptions to operations and the loss of critical information and data,” as cited by the official website. It spreads through phishing emails, fraudulent downloads, clicks on ads, or visits to websites hosting this malware, which installs code on the infected computer, preventing the user from accessing their own files.
Obviously, in the face of these threats, backups and protection systems are essential. But what happens then in manufacturing plants when faced with the threat of ransomware? Cyber threats lead to unscheduled shutdowns, downtime, and disruptions that are extremely costly for assembly-line manufacturers and mass-production companies; they compromise the security of the plant itself, endanger the physical safety of workers and the environment, and severely disrupt the supply chain. Every data exchange point is a gateway for cyberattacks.
The danger of these attacks lies not only in disrupting production but also in stealing intellectual property and intangible assets (brands, blueprints, manuals, and all types of information of extremely high commercial value).
Interconnectivity in OT/IoT environments increases the risk of malware infiltration. The most vulnerable points are typically found in the supply chain and among intermediaries, and attacks have been on the rise in Europe, Latin America, and East Asia. The damage caused by cyberattacks also impacts on the company’s image and relationships of trust with suppliers and customers, seriously undermining its credibility, with all the associated costs that this entails.
Meanwhile, the company sophos.com conducted a survey in late 2024, which concluded that 65% of respondents were victims of ransomware, 74% of attacks encrypted data, 53% of backup breaches were successful, and more than 60% of victims paid the ransom for their data. Read the full report here .
Other Types of Cyberattacks
In addition to ransomware, other types of cyberattacks have been identified, as noted in the article Artificial Intelligence-Based Cyber Security in the Context of Industry 4.0—A Survey (1) , which can be read in full here and compiles the following types of cyberattacks:
- Application protocol attacks
- Attacks Against Machine Learning and Data Analytics (reduce reliability and generate malicious behavior)
- Response and Measurement Injection Attacks (alter content during transmission from server to client)
- Time delay attacks (create discretionary delays and generate instability)
- Spoofing attacks (impersonating an identity to access control mechanisms)
- Privilege Escalation (bypassing authentication to access critical assets or services)
- Phishing and Spear Phishing attacks (data theft and scams via email; employees are seen as a vulnerability)
- False Sequential Logic attacks (direct attacks on the SCADA system)
- Deception attacks and False Data Injection attacks (sending false information between sensors and controllers)
- Poisoning and Evasion attacks (inserting incorrect data into the neural network, affecting the DL algorithm’s prediction)
- DDoS attacks (freezing and temporarily halting service by sending massive amounts of data)
- Zero-Day attacks (attacks exploiting new undisclosed not patched vulnerabilities)
- Advanced Persistent Threat (exploiting Zero-Day attacks to steal information or conduct industrial espionage)
- Man-in-the-Middle attacks and Eavesdropping attacks (misrouting communication between devices to damage the manufacturing company’s physical product)
- Information Modification(directly attacking the AI of robotics, altering its ability to distinguish images and compromising its accuracy)
How to protect factories, plants, and people? Here’s what the experts say
When malware attacks a company’s IT systems, the financial, reputational, or industrial espionage damages are very serious. But when the attack affects the interconnected OT ecosystem, the damage is worse, as people’s physical safety and lives, as well as environmental safety, are also at stake.
Cybersecurity experts recommend developing a comprehensive cybersecurity policy that addresses several key areas:
- Create system recovery strategies and test them
- Since supply chains are one of the weakest links, cybersecurity standards must be rigorous in this area.
- Protection systems must operate in an integrated manner, encompassing the cloud, OT, IT, personnel, etc.
- Pay special attention to exposed legacy systems (they are a natural gateway for malware)
- Continuous monitoring of network traffic, use of specialized OT firewalls
- USB sanitization stations (USBs are natural vectors for malware infection and remain the primary source of contamination in 2026)
- Workflow visibility for everyone: maintenance teams, suppliers, and all personnel involved in production areas.
- Scalable cybersecurity plans
- Constant education and awareness training for all OT personnel
- Each device or asset must have a unique identity, a requirement for authenticating its communications
- Segmentation between OT and IT networks and the use of security layers between the internet and hardware. (More info here)
Adaptive Cybersecurity for Connected Plans
The rapid growth of connectivity, the IoT, and Big Data significantly increases the attack surface for cyberattacks. Some experts believe that cybersecurity begins at the stage of OT system specifications, just as reliability is built in from the design and specifications of assets and systems. A program that encompasses both systems and people, offline backups, among other aspects. However, other authors consider this to be “a distraction,” since AI-generated malware spreads rapidly via USB drives, work emails, and other methods that are part of daily life in assembly and manufacturing plants.
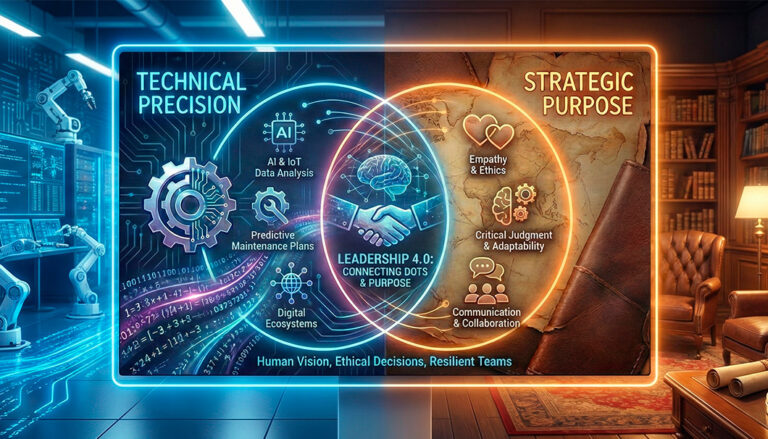
In addition to the expert recommendations outlined above, Adaptive Cybersecurity has become one of the most common solutions in the manufacturing industry for addressing cyberattacks. This system uses AI to monitor the entire attack surface to identify anomalous patterns, helping the SOC adapt to threats to ensure rapid and effective responses.
In this regard, the consulting firm Gartner outlines The Four Stages of an Adaptive Security Architecture, which consists of:
At present, being 100% invulnerable to cyberattacks is not possible. However, organizations can establish scalable cybersecurity protocols by using AI to predict attacks and implementing mechanisms to isolate malware within their OT/IoT ecosystems. The most important thing is to maintain visibility into your entire system and data traffic, measure the effectiveness of your cybersecurity mechanisms, constantly monitor your digital ecosystems, and adopt a reliability-focused approach where cybersecurity is also part of the corporate culture.
If you like this article, please share this information. To read more, please visit https://assetmanagementprofessionals.org/news-articles/ and see everything the Association of Asset Management Professionals has to offer its international maintenance and asset management community.
Sources:
- (1) Antonio João Gonçalves de Azambuja (Aeronautics Institute of Technology (ITA), Brazil), Christian Plesker (Product Life Cycle Management, Germany), Klaus Schützer (Production Engineering, Brazil), Reiner Anderl (Product Life Cycle Management, Germany), Benjamin Schleich (Product Life Cycle Management, Technische Universität Darmstadt, Germany), and Vilson Rosa Almeida (Graduate School, Aeronautics Institute of Technology (ITA), Brazil)